The cryptocurrency industry is witnessing a significant surge of interest surrounding the Midnight network, a platform engineered to strike a delicate equilibrium between user privacy, functional utility, and robust security. At its core, Midnight (NIGHT) operates as a privacy-first blockchain, empowering users with unprecedented control over their sensitive data while simultaneously facilitating private transactions, robust digital identity solutions, and compliant smart contract interactions. This in-depth exploration moves beyond the initial excitement to demystify the Midnight network, delineate its operational mechanics, and articulate the multifaceted problems it aims to resolve, thereby equipping potential investors with the insights necessary to evaluate the NIGHT token.
Understanding Midnight (NIGHT): A New Paradigm in Blockchain Privacy
Traditionally, public blockchains like Bitcoin and Ethereum, while celebrated for their transparency and auditability, present a significant limitation: the pervasive exposure of virtually all transactional data, wallet balances, and smart contract activities on a public ledger. This inherent transparency, while beneficial for verifying the integrity of operations, poses considerable challenges for applications dealing with sensitive information, proprietary business logic, or confidential user data.
Midnight addresses this critical vulnerability by introducing the concept of "programmable privacy." This innovative model allows data to remain confidential yet verifiable on-chain. Instead of broadcasting every detail, applications built on Midnight can selectively disclose only the information deemed necessary for public scrutiny. This nuanced approach ensures that sensitive data remains shielded while still allowing for the necessary validation and auditability required by many industries.
The native token of the Midnight ecosystem is NIGHT, which serves a dual purpose as a governance token and a security mechanism for the chain. Furthermore, NIGHT plays a crucial role in enabling participation in network-wide decision-making processes. Midnight’s tokenomics introduce a unique dual-token model, a departure from the single-token systems prevalent in most blockchain networks, which warrants a closer examination to fully grasp its implications.
The Current Momentum: Why Midnight is Capturing Attention
The burgeoning interest in Midnight (NIGHT) can be attributed to several converging factors within the cryptocurrency and broader technology landscapes:
- Growing Demand for Privacy Solutions: With increasing concerns about data breaches, surveillance, and the need for regulatory compliance in digital interactions, the demand for robust privacy solutions in the blockchain space is at an all-time high. Midnight’s foundational commitment to privacy positions it as a compelling alternative to existing, less privacy-centric platforms.
- Advancements in Zero-Knowledge Proofs (ZKPs): The underlying technology enabling Midnight’s privacy features, Zero-Knowledge Proofs, has seen significant maturation and adoption. As ZKPs become more efficient and accessible, their application in real-world blockchain scenarios, like those envisioned by Midnight, becomes increasingly viable and attractive to developers.
- Focus on Compliant and Enterprise Use Cases: Unlike many privacy-focused projects that cater primarily to individual anonymity, Midnight is actively targeting enterprise and regulated industries by enabling "compliant privacy." This means offering privacy without sacrificing the ability to meet stringent regulatory requirements, opening doors to sectors previously hesitant to adopt blockchain technology due to privacy and compliance concerns.
- Strategic Roadmap and Development Milestones: The anticipation surrounding Midnight’s upcoming federated mainnet launch and subsequent development phases, including cross-chain interoperability, signals a tangible progression towards a fully functional ecosystem. Such milestones generate optimism and attract attention from investors and developers alike.
Deconstructing Midnight’s Architecture: How it Works
Midnight’s innovative approach to privacy is rooted in its architectural design, which effectively separates the network’s consensus layer from its private computation layer.

The Dual-Layered Approach:
- Consensus Layer (Public): This layer is responsible for the core functionalities of any blockchain: ensuring immutability, maintaining the integrity of the ledger, and facilitating staking for network security. All activities on this layer are publicly verifiable, providing the foundational security and transparency expected from a blockchain.
- Private Computation Layer (Encrypted): This layer is where sensitive data is processed and stored locally on users’ devices. It operates independently of the public ledger, ensuring that confidential information is not broadcast across the network. This separation is key to Midnight’s ability to offer privacy without compromising the blockchain’s fundamental security.
This architectural separation allows Midnight to achieve a state where data can be both private and verifiable on-chain. Applications can dynamically decide which data elements are exposed and which remain encrypted, offering a level of control previously unattainable on public blockchains.
The Power of Zero-Knowledge Proofs (ZKPs)
At the heart of Midnight’s privacy-preserving capabilities lie Zero-Knowledge Proofs (ZKPs). ZKPs are a cryptographic method that allows one party (the prover) to prove to another party (the verifier) that a given statement is true, without revealing any information beyond the validity of the statement itself.
In the context of Midnight, ZKPs, specifically implemented through its Kachina protocol using zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge), enable developers to define precise granularities of data disclosure. This means:
- Verifiable Claims without Disclosure: A user can prove they possess sufficient funds for a transaction or meet specific eligibility criteria without revealing their exact wallet balance, personal identification details, or any other sensitive attribute.
- Scalable Smart Contract Interactions: The use of ZKPs, particularly through advancements like zk-Rollups, can significantly enhance the scalability of smart contract executions. By performing computations off-chain and submitting concise proofs to the main chain, Midnight can handle a high volume of transactions while maintaining strong security and confidentiality.
Why ZKPs are Crucial for Privacy and Compliance
The implications of ZKPs extend far beyond mere anonymity. Their ability to facilitate verifiable statements without revealing underlying data is transformative for several key industries:
- Financial Services: ZKPs can enable private, yet auditable, financial transactions. This is crucial for complying with Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations while protecting customer data from exposure. Imagine proving you are over 18 to access a service without revealing your date of birth, or proving you have sufficient credit for a loan without disclosing your full financial history.
- Healthcare: Sensitive patient records can be protected. For instance, a patient could prove they have a specific condition to qualify for a treatment without disclosing their full medical history.
- Digital Identity Management: ZKPs are foundational for creating self-sovereign identity solutions. Users can control their digital identities and selectively share verifiable credentials without compromising their privacy.
- Regulatory Compliance: Many industries are bound by strict data protection laws (e.g., GDPR, CCPA). ZKPs offer a technological pathway to achieve compliance by allowing verifiable attestations without the need to share raw, sensitive data.
- Enhanced Blockchain Scalability: As mentioned, ZKPs are a cornerstone of scaling solutions like zk-Rollups, which bundle multiple transactions off-chain and submit a single, verifiable proof to the mainnet. This significantly reduces transaction fees and increases throughput, a critical challenge for many blockchain networks.
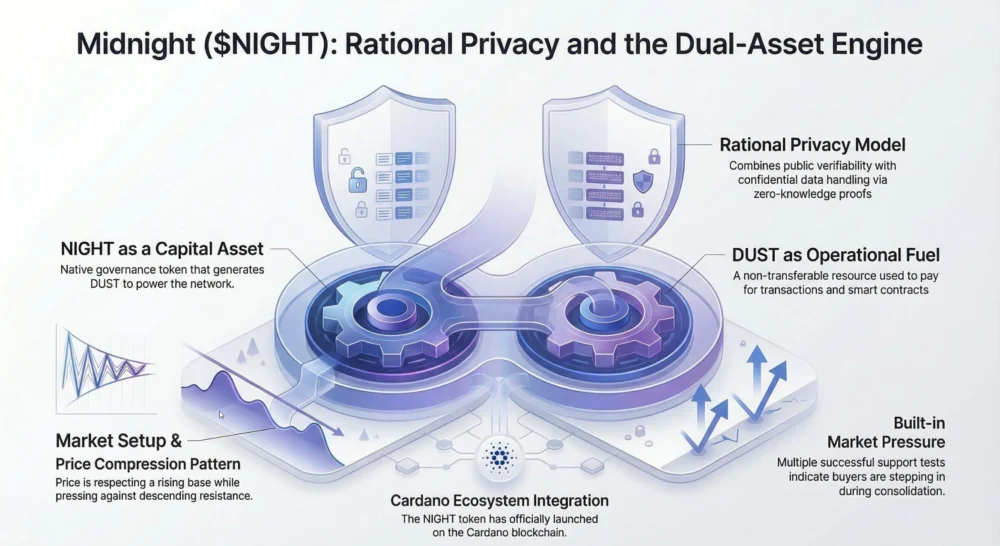
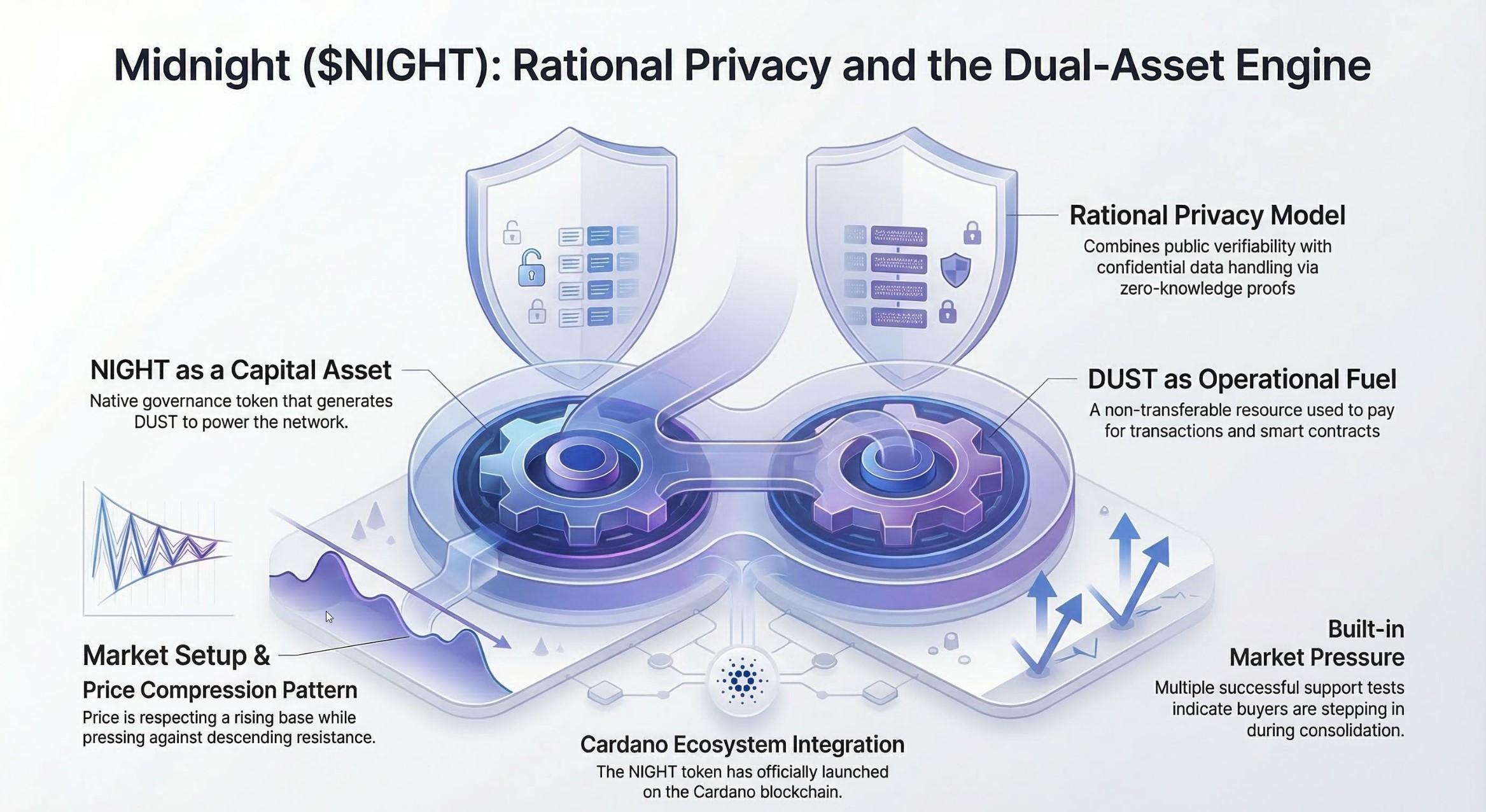
Midnight’s Innovative Dual-Token Model: NIGHT and DUST
A defining feature of Midnight’s architecture is its departure from the conventional single-token model. Instead, it employs a dual-token system comprising NIGHT and DUST, each serving distinct yet complementary roles:
-
NIGHT Token: This is the primary utility and governance token of the Midnight network.
- Governance: NIGHT holders have the right to vote on protocol upgrades, network parameters, and treasury allocations, empowering the community to shape the future of the platform.
- Staking: NIGHT can be staked to secure the network and participate in the consensus mechanism, earning holders rewards for their contribution.
- DUST Generation: A key function of NIGHT is its ability to generate DUST, a renewable resource essential for transaction fees.
-
DUST Token: DUST is designed as a utility token specifically for paying transaction and smart contract execution fees on the Midnight network.
- Renewable Resource: Unlike traditional gas tokens that are consumed and require repurchase, DUST functions more like a rechargeable battery. Holding and staking NIGHT automatically generates DUST, ensuring a continuous supply for network operations.
- Non-Transferable: DUST cannot be traded on exchanges or transferred between wallets. Its sole purpose is to fuel the execution of smart contracts and transactions within the Midnight ecosystem. This design prevents speculative trading of the fee token and ensures a predictable cost of operations for users.
This dual-token model aims to decouple network security and governance from transaction costs, potentially leading to a more stable and predictable user experience. By generating DUST through NIGHT holdings, users are incentivized to participate in network security and governance, creating a virtuous cycle that strengthens the ecosystem.
NIGHT Tokenomics: A Foundation for Value and Utility
The NIGHT token is central to the economic and governance framework of the Midnight network. Its tokenomics are designed to foster long-term value and utility:
- Fixed Supply: NIGHT has a capped total supply of 24 billion tokens. This scarcity mechanism is a common feature in cryptocurrency tokenomics, designed to prevent inflation and potentially support price appreciation as demand grows.
- Circulating Supply: Currently, approximately 16.6 billion NIGHT tokens are in circulation. The difference between the total and circulating supply represents tokens that are either vested, locked for future distribution, or allocated for ecosystem development. Understanding unlock schedules and vesting periods is crucial for investors to assess potential price pressure.
- Primary Functions: As previously outlined, NIGHT is primarily used for:
- Network Security: Staking NIGHT is essential for validators to participate in the consensus mechanism, ensuring the integrity and security of the blockchain.
- Governance: Token holders can actively participate in decision-making processes that guide the evolution of the Midnight protocol.
- DUST Generation: Staking NIGHT is the direct method for generating DUST, the fuel for network transactions. Stakers earn not only transaction fee capacity but also potentially other network rewards.
For a comprehensive understanding of NIGHT’s allocation, distribution strategies, and incentive mechanisms, interested parties are directed to the official Midnight tokenomics and incentives whitepaper. This document typically provides detailed breakdowns of how tokens are distributed among founders, early investors, public sales, marketing, and ecosystem development, offering critical insights into the token’s long-term economic viability.
Addressing Real-World Challenges: Midnight’s Potential Applications
The unique capabilities of the Midnight network position it to solve several persistent problems across various sectors:
- Confidential Enterprise Transactions: Businesses can conduct sensitive inter-company transactions, supply chain logistics, or financial settlements with the assurance that proprietary data remains private, while still being verifiable by authorized parties.
- Secure Digital Identity and KYC/AML: Midnight can underpin robust digital identity solutions that allow users to control their personal data. This is particularly relevant for financial institutions needing to perform KYC/AML checks without compromising user privacy. For instance, a user could prove their identity to a decentralized exchange without revealing their full name or address to the platform itself, only to a trusted verification entity.
- Private DeFi and Financial Instruments: The creation of private decentralized finance (DeFi) applications becomes feasible. This could include private lending protocols, confidential asset management, or privacy-preserving stablecoins, catering to users and institutions who require a higher degree of financial privacy.
- Data Monetization with Privacy: Individuals could potentially monetize their data for research or advertising purposes, granting specific permissions for its use while retaining ownership and control, thus enabling a more equitable data economy.
- Compliant Data Sharing in Regulated Industries: Healthcare providers could share anonymized patient data for research with verifiable privacy guarantees, or financial regulators could audit transactions without accessing sensitive customer information.
The Horizon: The Future Trajectory of Midnight
Midnight’s roadmap is ambitious, aiming to establish itself as a cornerstone privacy layer for the burgeoning Web3 ecosystem. Key upcoming developments include:
- Federated Mainnet Launch (Late March 2026): This pivotal event marks the transition from test environments to a production-ready blockchain. Early private smart contracts and decentralized applications (dApps) are expected to go live on the mainnet, showcasing the platform’s capabilities.
- Decentralization Expansion: Midnight plans to enhance decentralization by encouraging validator participation, with a particular focus on attracting established entities like Cardano stake pool operators. This move aims to foster a robust and resilient validator network.
- Cross-Chain Interoperability (Late 2026): A significant objective is to achieve full interoperability with other major blockchain ecosystems, such as Ethereum and Solana. This would enable the development of hybrid applications that can function across multiple chains while retaining Midnight’s privacy features, unlocking new possibilities for dApp development and user engagement.
From a market perspective, the successful execution of this roadmap could lead to significant appreciation for the NIGHT token as its utility becomes demonstrably proven. However, potential investors must remain cognizant of inherent risks, including:
- Market Volatility: The cryptocurrency market is notoriously volatile, and NIGHT’s price will be subject to broader market trends and sentiment.
- Supply Unlocks: As with many crypto projects, large token supply unlocks or vesting schedule expirations can introduce selling pressure, impacting the token’s price.
- Developer Adoption and Real-World Use Cases: The ultimate success of Midnight hinges on its ability to attract a vibrant developer community and foster the creation of compelling real-world applications that leverage its unique privacy features. Competition from established privacy-focused chains and emerging ZK solutions also presents a challenge.
Conclusion: Evaluating an Investment in Midnight (NIGHT)
The decision to invest in NIGHT ultimately rests on an individual’s conviction in the growing importance of privacy as a foundational element of blockchain technology. Midnight is addressing genuine limitations inherent in public blockchains, such as the exposure of sensitive data, regulatory friction, and the inadequacy of current privacy models for many enterprise use cases. The network’s deliberate focus on private smart contracts, digital identity solutions, and compliant applications holds the potential to attract a significant user base, including developers and enterprise clients.
However, it is imperative to reiterate that investing in any cryptocurrency token, including NIGHT, carries substantial risks. Extreme market volatility is a constant factor in the crypto space. Furthermore, supply unlocks and vesting schedules can exert downward pressure on token prices. Critically, the network must still definitively prove its product-market fit and demonstrate sustained adoption.
Therefore, if one chooses to invest in NIGHT, it is paramount to ensure that such an investment aligns with their personal risk tolerance and broader investment strategy. The guiding principle should always be to invest only what one can afford to lose.
Frequently Asked Questions (FAQs)
Is NIGHT a good investment?
The investment potential of NIGHT is contingent upon an investor’s risk appetite and their belief in the fundamental role of privacy in the future of blockchain. Currently, there is speculative upside tied to the upcoming mainnet launch in March 2026. However, significant risks remain, including market volatility, potential price impacts from token unlocks, and the competitive landscape of established and emerging ZK-focused chains. The prevailing bearish sentiment in the market suggests that a cautious approach, potentially waiting for post-launch stability rather than immediate acquisition, might be prudent for risk-averse investors.
What is the NIGHT token price prediction for 2026?
Price predictions for NIGHT in 2026 are varied, with optimistic outlooks suggesting significant potential if the mainnet launch is successful and utility grows. Bearish scenarios predict potential price dips to the $0.04-$0.05 range. Conversely, optimistic projections anticipate trading prices between $0.13 and $0.35 by the end of 2026. A more moderate average forecast hovers around $0.05-$0.07, factoring in the impact of token unlocks. Achieving higher price targets would necessitate robust growth in network utility and adoption.
How is Midnight different from Monero and Zcash?
Monero and Zcash are recognized as pioneering privacy coins, primarily focused on obscuring nearly all transactional details by default through sophisticated cryptographic methods. Midnight distinguishes itself by adopting a "selective disclosure" approach. Leveraging advanced zero-knowledge proofs, Midnight enables applications to conceal sensitive data while simultaneously allowing for the controlled revelation of specific information necessary for regulatory compliance, auditing, or to facilitate complex business logic. This nuanced approach offers greater flexibility for applications operating in regulated environments.
Where can I buy a NIGHT token?
NIGHT tokens can be acquired through several major centralized exchanges (CEXs), including prominent platforms such as OKX, Bybit, KuCoin, Gate.io, and Binance. Additionally, NIGHT is available on select decentralized exchanges (DEXs) via Cardano bridges, offering alternative avenues for purchase.