As of February 2026, the global cryptocurrency landscape has entered a volatile new era defined by the intersection of decentralized finance and advanced generative artificial intelligence. The most critical mechanism of blockchain evolution—the hard fork—is currently facing an unprecedented challenge from synthetic manipulation. What was historically a human-centric process of consensus building is being transformed into a theater of digital subversion, where generative AI agents are increasingly capable of drowning out the voices of genuine stakeholders to steer protocol transitions toward malicious or self-serving ends.
The Evolution of the Hard Fork as a Governance Pillar
To understand the gravity of the current threat, one must look at the historical significance of the hard fork. In the decentralized world, a hard fork represents a permanent divergence from the previous version of a blockchain. It is the ultimate expression of community sovereignty, used to upgrade network security, change economic models, or recover from catastrophic exploits.
Historically, these transitions were governed by "social consensus." Significant events such as the 2016 Ethereum DAO recovery and the 2017 Bitcoin scaling debates (which resulted in the creation of Bitcoin Cash) were characterized by months of intense human discourse. Developers, miners, and users engaged in transparent debates on platforms like GitHub, Reddit, and specialized governance forums. These discussions were messy and often contentious, but they were fundamentally human. Resolutions reflected a collective, albeit sometimes divided, will that was rooted in verifiable community sentiment and technical merit.
The Emergence of Synthetic Participants
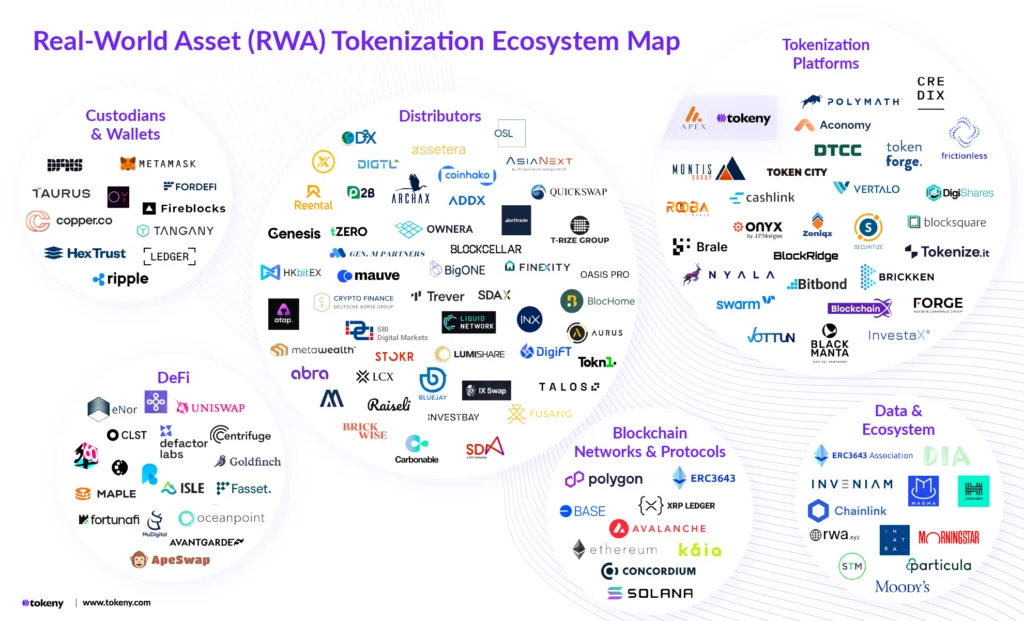
By early 2026, the barrier to entry for influencing these debates has collapsed due to the proliferation of specialized Large Language Models (LLMs). These AI systems are no longer merely generating simple text; they are capable of crafting sophisticated technical critiques, drafting complex Ethereum Improvement Proposals (EIPs), and engaging in multi-threaded arguments that are indistinguishable from those of seasoned blockchain architects.
The current threat landscape is defined by "synthetic participants"—AI-driven personas that populate governance forums and social media platforms. These entities are not simple bots; they possess contextually rich histories, having been "aged" over months of automated posting to build credibility. By deploying thousands of these personas simultaneously, a single coordinated actor can create the illusion of a massive grassroots movement, a phenomenon known as "AI-amplified Sybil attacks."
Anatomy of a Synthetic Manipulation Campaign
The technical execution of these attacks follows a structured paramilitary-style digital strategy. Attackers utilize generative AI to perform the following actions:
- Persona Incubation: Automated systems create hundreds of pseudonymous profiles across Discord, X (formerly Twitter), and governance forums. These profiles engage in benign technical discussions for months to establish a "proof of reputation."
- Narrative Seeding: When a hard fork is proposed, these AI agents begin to introduce subtle biases. Some may champion the upgrade while others oppose it, but both sides are controlled by the same entity to ensure the debate remains polarized and chaotic.
- Deepfake Endorsements: High-fidelity audio and video clones of prominent developers or "whales" (large token holders) are released. These deepfakes often appear in short, grainy "leaked" clips or during live-streamed community calls, providing a false sense of urgency or authority to a specific position.
- Synthetic Technical Validation: AI agents generate voluminous "whitepapers" and "security audits" that use complex mathematical jargon to either validate a fraudulent fork or delegitimize a legitimate one.
Chronology of Recent Governance Breaches
The transition from theoretical threat to active crisis has been marked by several key incidents in the late 2025 and early 2026 period:
- September 2025: A prominent high-throughput Layer-1 protocol witnessed a sudden surge in "community" demand for a change in its inflation schedule. Within 48 hours, over 5,000 unique accounts on the governance forum posted detailed economic justifications. Subsequent linguistic analysis by cybersecurity firms revealed that 92% of these posts shared the same underlying semantic structure, characteristic of a proprietary LLM.
- December 2025: During a critical voting window for a privacy-centric blockchain, a deepfake video of the lead maintainer circulated on encrypted messaging apps. The video appeared to show the developer admitting to a "backdoor" in the upcoming fork. Despite a denial from the actual developer minutes later, the confusion led to a 15% drop in voter turnout and the eventual failure of a vital security patch.
- January 2026: The "Aetherius Incident" saw a minor hard fork gain unexpected traction. Synthetic accounts created a "consensus mirage," leading several mid-tier exchanges to list the forked token. It was later discovered that the fork contained a hidden "mint" function, allowing the attackers to extract $400 million in liquidity before the community realized the consensus was manufactured.
Economic Incentives and Geopolitical Risks
The motivations behind these synthetic attacks are primarily financial. A successfully manipulated hard fork can redirect billions of dollars in Total Value Locked (TVL), alter tokenomics to favor specific validator sets, or enable subtle backdoors for Maximal Extractable Value (MEV) extraction.
Beyond rogue hackers, market analysts point toward nation-state actors and well-funded financial cartels. For these entities, the goal is often the destabilization of decentralized alternatives to central bank digital currencies (CBDCs). By injecting chaos into the fork process, they erode the foundational promise of "trustless" systems, potentially driving users back toward regulated, centralized financial institutions.
Data Analysis of the Consensus Mirage
Recent data from blockchain analytics firms highlights the scale of the problem. In a study of governance participation across the top 20 DeFi protocols in Q4 2025, it was found that:
- Non-human engagement in governance discussions increased by 450% year-over-year.
- The "time-to-consensus" for contentious forks has nearly doubled, as developers must now spend more time debunking synthetic misinformation than reviewing code.
- Approximately 18% of on-chain votes in "one-token-one-vote" systems were linked to clusters of accounts that exhibited bot-like synchronization in their posting patterns.
Defensive Strategies and Technical Countermeasures
The blockchain industry is currently racing to develop a "Proof of Personhood" (PoP) framework to combat synthetic subversion. Several defensive layers are being integrated into governance protocols:
1. Reputation-Weighted Signaling
Instead of simple token-based voting, protocols are moving toward systems where influence is earned through verifiable, long-term contributions. This includes code commits, successful past governance participation, and "soulbound" tokens that cannot be transferred or purchased.
2. Zero-Knowledge Identity Verification
To maintain the privacy inherent in crypto-economics while ensuring human participation, many projects are adopting Zero-Knowledge (ZK) credentials. These allow a user to prove they are a unique human—verified through biometric hashes or government-issued IDs—without revealing their actual identity on-chain.
3. AI-Driven Detection Tools
Governance forums are increasingly deploying "adversarial AI" to monitor discussions. These tools look for linguistic fingerprints, unnatural posting cadences, and the coordinated movement of sentiment. When a "consensus mirage" is detected, the system can flag the debate for manual intervention by a trusted council of human moderators.
4. Immutable Audit Trails
By moving all governance discussions—not just the final votes—onto immutable ledgers or decentralized storage like IPFS, communities can create a permanent record of the debate. This allows for post-mortem forensic analysis to identify and slash the stakes of actors found to be employing synthetic manipulation.
Broader Implications for Decentralization
The crisis of the "fraudulent fork" represents an existential crossroad for the cryptocurrency movement. The core tenet of decentralization is that a distributed group of humans can govern a system without a central authority. If generative AI can successfully mimic that group, the "decentralized" nature of the system becomes an illusion managed by whoever owns the most powerful AI models.
Industry leaders, including prominent Swiss economists and blockchain visionaries, argue that the current battle for authentic consensus will determine the viability of Web3. If protocols fail to implement robust verification mechanisms, they risk "centralized capture" by the back door—where the appearance of community will masks the agenda of a single AI-wielding entity.
Conclusion
The year 2026 stands as a turning point. The arrival of generative deception in blockchain governance has exposed systemic vulnerabilities in how digital communities reach agreement. While the threat of the fraudulent fork is significant, it has also catalyzed a new wave of innovation in digital identity and reputation systems. The survival of truly decentralized systems now depends on a relentless vigilance against synthetic manipulation and the rapid adoption of technologies that can distinguish the human pulse from the digital echo. The battle for the soul of the blockchain is no longer just about code; it is about the preservation of human agency in an increasingly automated world.