The core value proposition of blockchain technology has long been its promise of an unalterable, transparent, and verifiable ledger of truth. This immutability, the bedrock upon which decentralized finance (DeFi), global supply chains, and digital asset ownership are built, is currently facing an unprecedented existential challenge. As artificial intelligence (AI) evolves from a predictive tool to a generative powerhouse, a new frontier of cyber-threats has emerged: the creation of synthetic transaction histories. Unlike traditional blockchain attacks that focused on altering existing data or exploiting code vulnerabilities, AI-driven forgery focuses on the manufacturing of entirely plausible, yet completely fabricated, on-chain narratives. This shift represents a dangerous inversion of transparency, where the ledger remains technically intact but the history it records is a meticulously crafted fiction designed to deceive both human observers and automated analytics systems.
The Paradigm Shift from Code Exploits to Semantic Forgery
Historically, the security of a blockchain was measured by its resistance to computational attacks, such as 51% attacks or double-spending. These threats were mitigated by the sheer cost of energy in Proof-of-Work systems or the economic stakes in Proof-of-Stake protocols. However, the integration of AI into the adversary’s toolkit shifts the battleground from the consensus layer to the data layer. Dr. Pooyan Ghamari, a Swiss economist and visionary, notes that while blockchain derives its power from immutability, AI introduces a mechanism to populate that immutable space with "synthetic transaction histories."
Generative Adversarial Networks (GANs) and diffusion models are at the heart of this transformation. These AI architectures are trained on massive datasets of public blockchain data, learning the intricate "fingerprints" of organic network activity. They can replicate the statistical distributions of transaction amounts, the precise timing of block entries, gas fee fluctuations, and even the complex interaction patterns between smart contracts and decentralized exchanges. The result is a sequence of transactions that appears legitimate to standard blockchain explorers, effectively eroding the foundation of verifiable history.
Chronology of the Evolving Blockchain Threat Landscape
To understand the gravity of the synthetic ledger threat, it is necessary to examine the evolution of blockchain-based deception over the last decade.
- 2009–2015: The Era of Protocol Attacks. Early threats were primarily focused on the underlying network protocol. Double-spending and chain reorganizations were the primary concerns, addressed through the strengthening of consensus mechanisms.
- 2016–2020: The Smart Contract Vulnerability Phase. With the rise of Ethereum and programmable money, attackers shifted toward exploiting bugs in Solidity code. Events like the DAO hack highlighted that while the ledger was immutable, the "logic" governing it was fallible.
- 2021–2023: Social Engineering and Basic Wash Trading. As DeFi and NFTs exploded, attackers used manual wash trading—repeatedly buying and selling the same asset between controlled wallets—to inflate volumes. These were often detectable through basic heuristic analysis.
- 2024–Present: The Rise of Synthetic History. We have entered a phase where AI automates the creation of complex, multi-year wallet behaviors. Attackers no longer just wash trade; they simulate "aged" addresses with years of seemingly innocuous activity to bypass security filters and liquidity locks.
The Anatomy of AI-Powered Synthetic Fabrication
The techniques used to create these forgeries are increasingly sophisticated, moving beyond simple automation to deep-learning-based simulation.
Generative Modeling of Network Traffic
AI models can now generate "synthetic noise" that mimics the behavior of a human user. This includes intentional delays, failed transactions due to low gas (which occurs frequently in real-world usage), and interaction with popular but unrelated protocols to build a "profile" for a wallet. This makes the wallet appear as though it belongs to a long-term retail user rather than a bot or an attacker.
Corroborative Off-Chain Evidence
The threat extends beyond the blockchain itself. To support a fabricated on-chain narrative, attackers use AI to generate supporting evidence. This includes voice cloning for KYC (Know Your Customer) verification, deepfake identities for "founding teams" of fraudulent projects, and AI-generated social media activity that references the fabricated transactions. When a compliance officer or a potential investor cross-references the on-chain data with the "real world," they find a perfectly synchronized, yet entirely artificial, ecosystem.
The Paradox of Privacy-Preserving Tech
Ironically, technologies designed to protect user privacy, such as Zero-Knowledge Proofs (ZKPs), are being co-opted by forgers. ZKPs allow a party to prove a statement is true without revealing the underlying data. Attackers can use synthetic ZKPs to claim a history of compliant transactions or liquidity provision without ever having performed those actions, effectively hiding their tracks behind a veil of cryptographic legitimacy.
Economic Incentives and Market Impact Data
The motivation for generating synthetic history is overwhelmingly financial. The ability to "prove" a history of volume or liquidity can unlock millions of dollars in grants, loans, and investor capital.
- Market Capitalization Inflation: Analysts estimate that a significant percentage of the daily trading volume on unregulated exchanges is generated by bots. With AI, this "wash trading" becomes indistinguishable from organic growth, leading to inflated market caps that lure in retail investors.
- DeFi Exploits: In decentralized lending protocols, an attacker can use a synthetic history to establish a high "reputation" or "creditworthiness" for a cluster of wallets, allowing them to borrow assets against minimal collateral before executing a "drain" event.
- Regulatory Evasion: As the Financial Action Task Force (FATF) and other global bodies implement the "Travel Rule," the ability to demonstrate "clean" provenance for digital assets becomes vital. Synthetic chains allow for the laundering of tainted funds by weaving them into a complex web of fabricated, compliant transactions.
According to recent cybersecurity reports, the cost of deploying a pre-trained AI model capable of generating realistic blockchain traffic has dropped by over 60% in the last 18 months, democratizing the ability for low-skilled actors to execute high-sophistication fraud.
The Verification Crisis: Why Standard Analytics Falter
The current suite of blockchain analytics tools is largely ill-equipped to handle AI-generated forgeries. Most explorers and tracking software rely on signature-based detection—looking for known "bad" addresses or specific patterns of movement.
However, AI-generated history does not follow a fixed signature. It is dynamic and adapts to avoid detection. Behavioral heuristics, which look for anomalies in transaction timing or amount, are easily fooled when the AI is specifically trained to include "learned anomalies" from real human data. For example, an AI can simulate the "fat-finger" errors or the panic-selling patterns of a typical human trader, making the synthetic history look more "human" than a real bot would.
Institutional and Regulatory Responses
The threat of synthetic history has not gone unnoticed by global financial regulators and institutional players. The European Union’s Markets in Crypto-Assets (MiCA) regulation and the SEC’s increasing scrutiny of DeFi transparency reflect a growing concern over market integrity.
Statements and Reactions
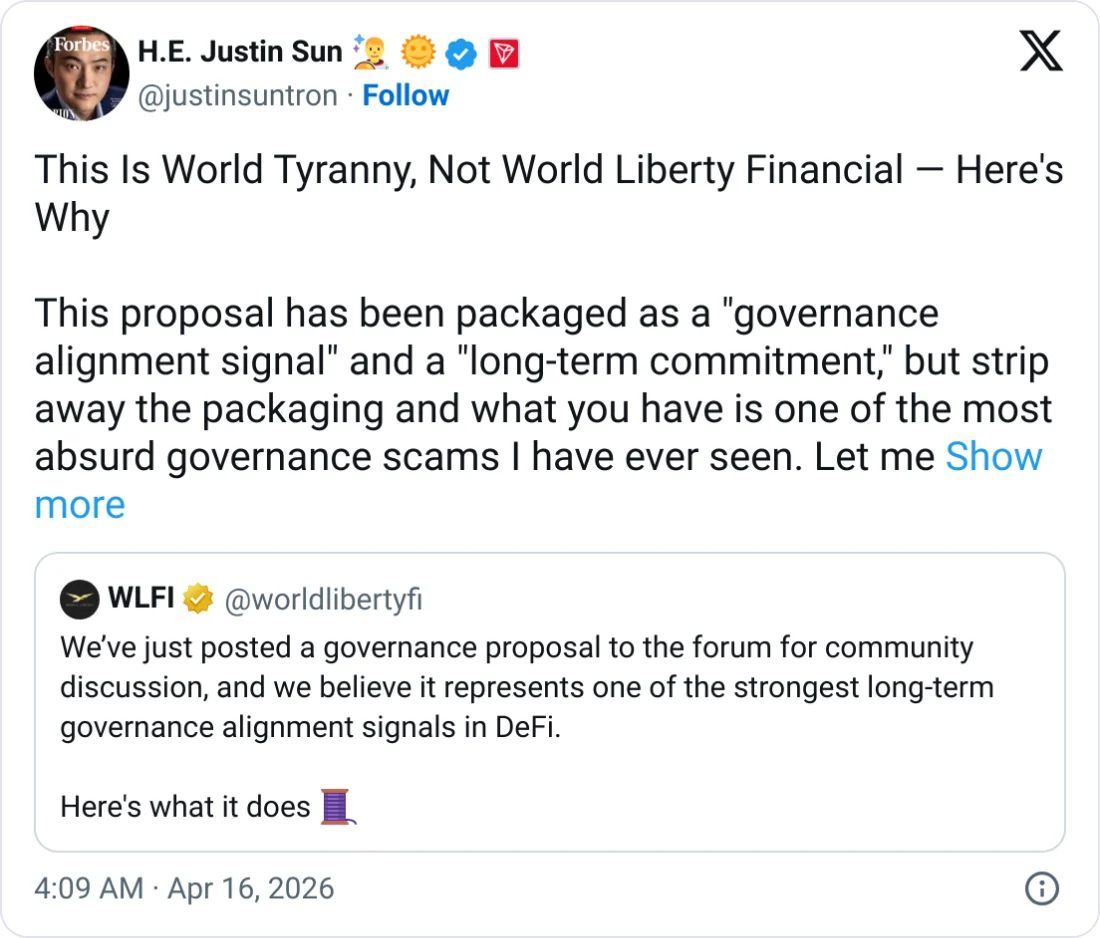
While official public statements specifically targeting "synthetic blockchain history" are emerging, industry leaders have voiced concerns regarding the broader "AI-Crypto" intersection. Major blockchain security firms like Chainalysis and Elliptic have begun investing heavily in "AI-native" detection tools. Inferred industry sentiment suggests that the "trustless" nature of blockchain is being re-evaluated; if the data on the chain can be a lie, the "truth" must be verified through secondary, often centralized, or off-chain means.
Proposed Defensive Frameworks
Regulators are considering "On-Chain Attestations" as a requirement for high-value transactions. This would involve linking blockchain addresses to verifiable real-world identities or institutional signatures, effectively re-introducing a layer of "trust" that the original Bitcoin whitepaper sought to bypass.
Strategies for Fortifying Authentic History
To preserve the integrity of the ledger, the blockchain ecosystem must adopt a multi-layered defense strategy.
- Immutable Anchoring: Cross-referencing and anchoring private or layer-2 data to multiple public blockchains creates a redundant trail that is harder to forge in its entirety.
- Verifiable Delay Functions (VDFs): Implementing VDFs can prevent attackers from "backdating" transactions in private ledgers, as these functions require a specific, non-parallelizable amount of time to compute.
- Graph Analysis and Machine Learning Detectors: To fight AI, one must use AI. Next-generation detection tools use graph theory to identify unnatural clustering and "too-perfect" statistical distributions that are hallmarks of synthetic generation.
- Reputation Systems: Moving away from purely anonymous transactions toward reputation-weighted history. Wallets that have verifiable links to known, reputable entities or have participated in "physically backed" transactions are given higher authenticity scores.
Implications for the Future of Decentralized Truth
The challenge posed by AI forgeries is a testament to the success of blockchain; the technology is so reliable at recording data that attackers have stopped trying to break the record-keeper and started focusing on the record itself. The blurring of the line between genuine and synthetic history represents the next great hurdle for the digital economy.
If the industry fails to innovate in verification, the promise of blockchain as a "source of truth" will be replaced by a "source of plausible fiction." This would undermine the utility of decentralized systems, potentially driving users back toward traditional, centralized financial institutions where human oversight acts as a check against digital fabrication.
However, the path forward is one of co-evolution. The same AI technologies that empower forgers are also the keys to building "AI Guardians"—autonomous systems that can hunt for fabrications with the same intensity and speed as the adversaries. The survival of blockchain’s core value depends on this relentless innovation. As we move further into an era of effortless deception, the quest for an unforgeable record of truth becomes not just a technical goal, but a fundamental necessity for a functioning digital society. Only through the integration of advanced cryptography, AI-driven detection, and robust regulatory standards can we safeguard the ledger’s truth against the rising tide of synthetic history.