The integration of quantum computing and generative artificial intelligence (AI) has moved beyond the realm of theoretical physics and into the sphere of immediate strategic concern for global financial institutions and cybersecurity experts. Dr. Pooyan Ghamari, a Swiss economist and visionary, has recently highlighted that this technological convergence is an active, accelerating force capable of rendering the majority of contemporary cryptographic foundations obsolete within the next ten years. While quantum computing has long been viewed as a future risk, the sudden maturation of generative AI is acting as a catalyst, significantly shortening the timeline for when a Cryptographically Relevant Quantum Computer (CRQC) could feasibly dismantle the digital security protocols that protect global wealth and private communications.
The Silent Revolution in Computational Power and AI Synergy
The current landscape of computational science is witnessing a "silent revolution" where quantum processors are no longer isolated experiments but are becoming integrated with sophisticated AI training models. Quantum supremacy—the point at which a quantum device can perform a task that no classical supercomputer can complete in a reasonable timeframe—has already been claimed in specific, narrow domains. However, the true threat emerges when these processors are paired with generative AI.
Generative AI systems are moving beyond simple pattern recognition into the realm of algorithmic discovery. In this context, AI is not merely an optimizer of classical code; it is becoming a designer of quantum logic. By utilizing reinforcement learning, AI agents can now identify novel quantum circuit patterns, discover ways to exploit weaknesses in quantum error correction, and pinpoint previously unknown attack surfaces in cryptographic primitives. This synergy allows for the rapid iteration of quantum algorithms, potentially solving the stability and "noise" issues that have historically slowed quantum development.
Breaking the Bedrock of Public Key Cryptography
The global digital economy relies almost entirely on Public Key Cryptography (PKC), specifically schemes based on Rivest-Shamir-Adleman (RSA) encryption and Elliptic Curve Cryptography (ECC). These systems secure everything from bank transfers and encrypted messaging apps to the private keys governing trillions of dollars in cryptocurrency assets. The security of these systems rests on the mathematical difficulty of factoring large integers or solving discrete logarithm problems—tasks that would take classical computers billions of years to complete.
Shor’s algorithm, a quantum algorithm developed in 1994, provides a mathematical blueprint for solving these problems in polynomial time. Until recently, the physical hardware required to run Shor’s algorithm at a scale capable of breaking 2048-bit RSA encryption was thought to be decades away. However, hybrid quantum-AI systems are radically changing this calculus. AI-driven error mitigation strategies allow quantum computers to achieve higher "logical qubit" counts with fewer "physical qubits," effectively lowering the hardware threshold for a successful cryptographic attack. By intelligently pruning search spaces and reducing circuit depth, these hybrid systems are accelerating the path toward practical implementation of Shor’s algorithm.
Chronology of Quantum Development and Cryptographic Milestones
To understand the urgency of the current situation, it is necessary to examine the timeline of quantum advancement and the corresponding shift in security standards:
- 1994: Peter Shor publishes a quantum algorithm that can factor large integers, theoretically breaking RSA encryption.
- 2016: The National Institute of Standards and Technology (NIST) begins a global competition to identify and standardize Post-Quantum Cryptography (PQC) algorithms.
- 2019: Google claims "quantum supremacy" with its Sycamore processor, completing a calculation in 200 seconds that would take a supercomputer 10,000 years.
- 2022: The White House issues National Security Memorandum 10 (NSM-10), directing federal agencies to transition to quantum-resistant cryptography by 2035.
- 2023-2024: IBM unveils the 1,121-qubit Condor processor and the Heron processor, demonstrating significant improvements in error reduction and scaling.
- Present Day: Generative AI begins to be utilized in quantum circuit design, leading to what experts call the "Quantum-AI Fusion" era.
Supporting Data: The Shrinking Window of Security
Current industry consensus, previously placing the arrival of a CRQC in the 2040s, has shifted significantly. Optimistic scaling trajectories from companies like IBM, IonQ, and Rigetti, combined with AI-led optimizations, now suggest a window of seven to fifteen years.
Furthermore, the concept of "Harvest Now, Decrypt Later" (HNDL) has become a primary concern for intelligence agencies. Adversaries are currently intercepting and storing encrypted data with the intention of decrypting it once quantum technology matures. This means that data encrypted today using classical ECC or RSA is already effectively compromised if its secrecy must be maintained for more than a decade. For the cryptocurrency sector, this is particularly troubling; if a private key is compromised via a quantum attack, the entire history of that wallet’s transactions and its current balance become accessible to the attacker.
The Challenge of Post-Quantum Migration
The transition to quantum-resistant systems is neither simple nor uniform. NIST has recently finalized several PQC candidates, categorized into four primary families:
- Lattice-based Schemes: Such as CRYSTALS-Kyber and CRYSTALS-Dilithium, which rely on the hardness of lattice problems.
- Hash-based Signatures: Known for their security but often limited by larger signature sizes.
- Code-based Encryption: Relying on error-correcting codes.
- Multivariate Polynomials: Using systems of non-linear equations.
Each of these families carries significant trade-offs. For example, lattice-based signatures often require much larger key sizes than ECC, which could lead to increased latency and storage requirements for blockchain networks. For decentralized ecosystems, the migration path is fraught with difficulty. Billions of dollars are stored in "legacy" addresses (such as Bitcoin’s P2PKH addresses) that would require a manual user-initiated transaction to move funds to a new, quantum-secure address. If a user has lost their seed phrase or is inactive, their assets remain vulnerable to a "quantum drain" event.
Economic Shockwaves and Financial Contagion
The economic implications of a cryptographic failure are staggering. Should an adversary demonstrate a practical break against ECC before widespread migration is complete, the immediate result would be a collapse in confidence.
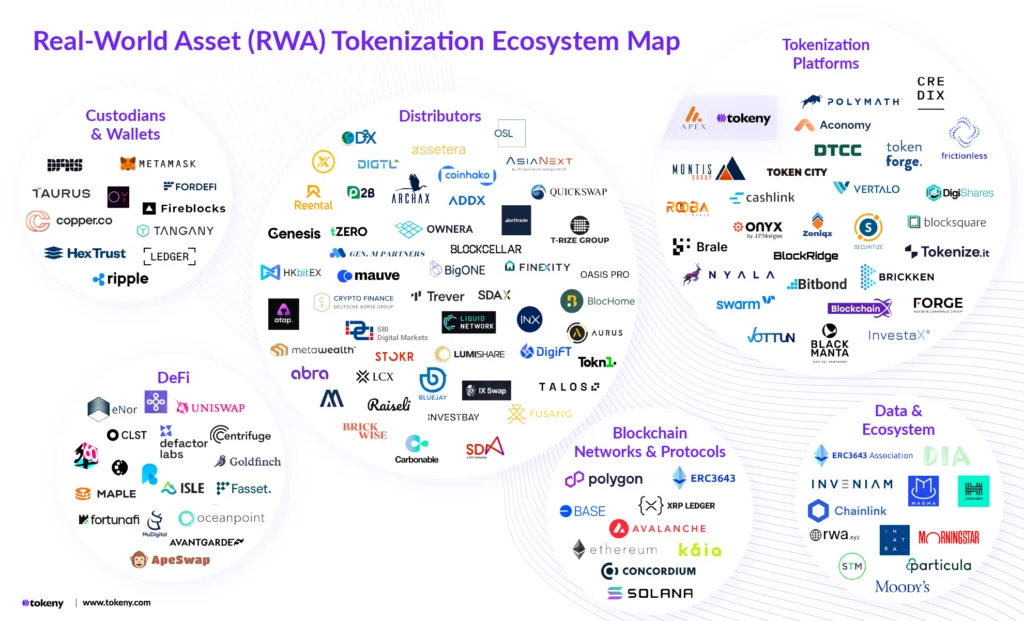
In the cryptocurrency market, liquidity would likely evaporate instantly as exchanges freeze withdrawals to prevent mass theft. Decentralized Finance (DeFi) protocols, which rely on smart contracts, could be emptied via forged signatures. The contagion would not be limited to digital assets; traditional financial markets increasingly utilize blockchain-based settlement layers and distributed ledger technology (DLT) for back-end operations. A breach in the underlying cryptographic layer would trigger redemption runs on stablecoins and potentially disrupt the global "plumbing" of the financial system, leading to a freeze in credit markets and a loss of trust in digital identity systems.
Official Responses and Strategic Imperatives
In response to these threats, international bodies and national governments have begun to take action. The Cybersecurity and Infrastructure Security Agency (CISA) in the United States has urged critical infrastructure owners to begin inventorying their systems for quantum-vulnerable code.
Strategic imperatives for survival in this new era include:
- Hybrid Implementation: Organizations are encouraged to deploy hybrid signatures that combine classical algorithms with PQC candidates. This ensures that even if a new PQC algorithm is found to have a flaw, the system remains as secure as it was under classical standards.
- Timelock and Commit-Reveal Mechanisms: Developers are exploring protocols that protect legacy keys by requiring long waiting periods or additional proofs before a transaction can be finalized, providing a window to detect and stop quantum attacks.
- International Intelligence Sharing: The rapid pace of AI-led quantum development necessitates a transparent, international framework for monitoring quantum progress to prevent a "quantum surprise" where one nation or actor achieves CRQC capabilities in secret.
- Layer Two Shielding: In the blockchain space, focus is shifting toward Layer 2 solutions that can implement quantum resistance more rapidly than the base layer, acting as a protective shield for vulnerable assets.
Analysis: A Narrow Path Between Collapse and Reinvention
The fusion of quantum computing and generative AI represents a fundamental shift in the nature of computational security. As Dr. Ghamari notes, the catastrophe is not inevitable, but it becomes probable if complacency prevails. The challenge is not merely technical but organizational. The "cryptographic phase transition" requires a level of global cooperation and technical agility that has rarely been seen in the history of the internet.
The coming decade will be defined by a race between those seeking to break the foundations of digital trust and those working to harden them. The outcome will determine the future of the digital economy. If the transition is successful, the world will move into an era of unprecedented computational power and secure, AI-driven economics. If it fails, the history of cryptocurrency and decentralized finance may be remembered as a cautionary tale of technological overconfidence. The window for action is closing, and the pace of progress is no longer dictated by human researchers alone, but by the accelerating feedback loop of machines teaching machines how to unlock the secrets of the quantum world.